Third-party vulnerability scanning is a proactive way to protect your SaaS ecosystem from security threats. It identifies risks in real-time, such as misconfigurations, expired SSL certificates, and compromised OAuth tokens, ensuring your supply chain remains secure. Key takeaways:
- Why it matters: By 2025, 30% of data breaches will involve third parties, with SaaS supply chain attacks costing an average of $4.91 million.
- How it works: Scanning maps dependencies, checks for vulnerabilities using databases like the NVD, and monitors SaaS integrations continuously.
- Risks addressed: Outdated software, insecure APIs, shadow IT, and misconfigured OAuth tokens.
- Recent examples: Salesloft-Drift breach (2025) and Shai-Hulud worm (2025) highlight the growing threat to SaaS ecosystems.
With automated tools, businesses can track vulnerabilities, prioritize fixes, and reduce risks from third-party integrations. This approach ensures real-time visibility and faster response to potential threats.
Securing the SaaS Supply Chain: A Practical Approach, Dinesh Chandrasekaran | FOSSASIA Summit 2025
sbb-itb-e3aed85
How Third-Party Vulnerability Scanning Works
How Third-Party Vulnerability Scanning Works: 3-Step Process
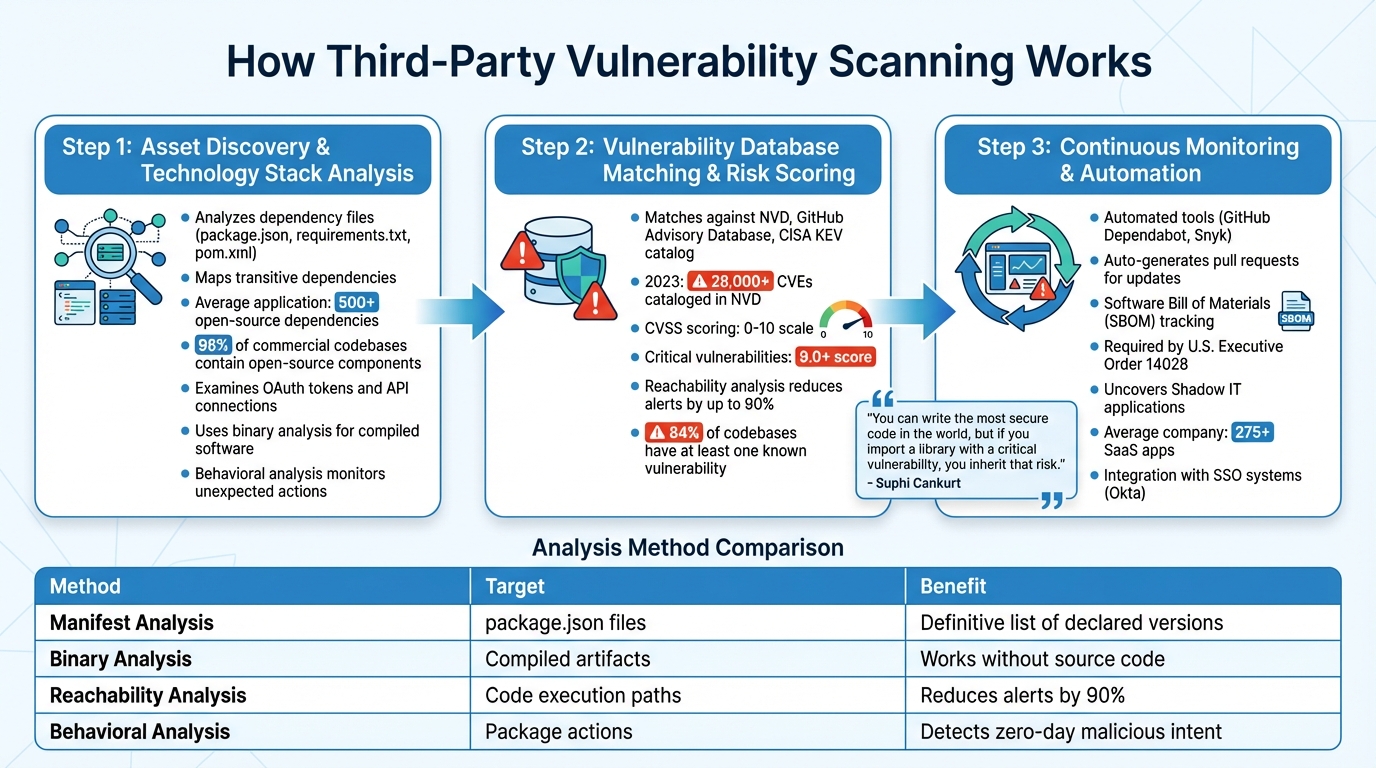
Third-party vulnerability scanning involves three key steps: identifying the software in your ecosystem, comparing it against known security issues, and continuously monitoring for new threats. Together, these steps provide a detailed picture of risks within your SaaS supply chain.
Asset Discovery and Technology Stack Analysis
The process starts by mapping out all the dependencies in your software. Scanners analyze files like package.json, requirements.txt, or pom.xml to list the third-party libraries your applications rely on. But the tricky part lies in managing transitive dependencies - those brought in automatically by the libraries you use. For instance, a single package can introduce dozens more. On average, applications include over 500 open-source dependencies, and 96% of commercial codebases contain open-source components. To address this complexity, scanners create a full dependency tree, capturing all connections.
Modern scanners go beyond code libraries, examining SaaS-to-SaaS integrations. They identify OAuth tokens and API connections between platforms like Salesforce, Slack, and Google Workspace. As mentioned earlier, compromised OAuth tokens can significantly expand your attack surface.
For compiled software or container images where source code isn't accessible, scanners use binary analysis. This method identifies components by examining compiled artifacts. Some advanced tools also use behavioral analysis, monitoring actions like unexpected network calls or file access to detect malicious code - even if it hasn’t been officially flagged as vulnerable yet.
With a complete dependency map in hand, scanners can then evaluate the security of each component.
Vulnerability Database Matching and Risk Scoring
Once the components are identified, scanners match them against public vulnerability databases. Key sources include the National Vulnerability Database (NVD), GitHub Advisory Database, and the CISA Known Exploited Vulnerabilities (KEV) catalog. In 2023 alone, the NVD cataloged over 28,000 CVEs.
Each vulnerability is rated using the Common Vulnerability Scoring System (CVSS), which assigns a score from 0 to 10. Critical vulnerabilities - those scoring 9.0 or higher - demand immediate attention. However, raw CVSS scores can be misleading because they don’t account for whether your application actually uses the vulnerable code.
This is where the dependency tree becomes essential. Advanced scanners use reachability analysis, leveraging static call graph analysis to determine if a vulnerable function is actively used in your application. This approach can reduce security alerts by up to 90%, helping teams focus on genuine risks instead of theoretical ones. As Suphi Cankurt, an AppSec enthusiast, explained:
"You can write the most secure code in the world, but if you import a library with a critical vulnerability, you inherit that risk."
- Suphi Cankurt, AppSec Enthusiast
The challenge is immense, as 84% of codebases containing open-source components have at least one known vulnerability. Without a way to prioritize, security teams risk being overwhelmed by alerts while overlooking the most pressing threats.
Continuous Monitoring and Automation
Once vulnerabilities are identified and prioritized, continuous monitoring ensures ongoing protection as your ecosystem evolves. A single scan isn’t enough. New vulnerabilities appear daily, and SaaS ecosystems are constantly changing as developers add integrations or update packages. Continuous monitoring shifts vulnerability management from a one-time task to an ongoing process.
Automated tools like GitHub's Dependabot or Snyk monitor for new vulnerabilities in your dependencies and can even generate pull requests to update affected packages, minimizing your exposure window. Additionally, modern scanning tools produce a Software Bill of Materials (SBOM), which lists every software component. When a new CVE is disclosed, you can cross-reference your SBOM instead of re-scanning your entire codebase. This approach is increasingly required, as U.S. Executive Order 14028 mandates SBOMs for federal software suppliers.
Automation also helps uncover Shadow IT - unsanctioned SaaS applications set up without IT’s approval. By integrating with single sign-on systems like Okta or analyzing financial data from platforms like NetSuite, scanners can identify all SaaS applications in use. With companies now averaging over 275 SaaS apps, manual tracking becomes impractical.
| Analysis Method | Primary Target | Key Benefit |
|---|---|---|
| Manifest Analysis | Dependency files (package.json, etc.) |
Provides a definitive list of declared versions |
| Binary Analysis | Compiled artifacts, container images | Identifies components when source code is unavailable |
| Reachability Analysis | Execution paths within code | Reduces alert noise by up to 90% |
| Behavioral Analysis | Package actions (e.g., network calls) | Detects malicious intent in zero-day packages |
Why SaaS Supply Chains Need Vulnerability Scanning
SaaS supply chains face threats that traditional security tools simply can't handle. Unlike older software systems protected by firewalls, SaaS applications connect through mechanisms like OAuth tokens, API keys, and service accounts. If attackers manage to compromise even one vendor in this web of connections, they can infiltrate hundreds of downstream environments - often without triggering any alarms.
To address these risks, organizations need proactive, automated security measures for their SaaS integrations. The speed of data transfers between SaaS apps - 10 times faster than human-driven processes - makes manual monitoring impractical. Patrick Opet, CIO at JPMorgan Chase, put it bluntly:
"Modern SaaS integration models are eroding decades of carefully architected security controls, collapsing authentication and authorization into overly simplistic trust relationships that attackers actively exploit."
The problem isn't limited to approved applications. Employees often connect unauthorized communication and collaboration tools with a single click, granting them access to sensitive company data without IT's knowledge. On top of that, 96% of commercial codebases rely on open-source components, which often include hundreds of hidden dependencies. Tracking these without automated scanning is nearly impossible.
Risks of Outdated Technologies and Misconfigurations
Outdated software and configuration errors are like open doors for attackers. If a component in your software's dependency tree isn’t updated, it likely contains known vulnerabilities that hackers can exploit with ease. Many of these vulnerabilities hide in fourth-party dependencies - elements your primary vendor’s software depends on.
Misconfigurations add another layer of risk. Exposed databases, unsecured API keys, or poorly configured OAuth settings can lead to immediate data breaches. Alarmingly, 46% of IT and business leaders have experienced breaches linked to a vendor after the partnership was already established. Under the shared responsibility model, SaaS vendors secure their platform infrastructure, but customers are responsible for securing connected apps and OAuth access. Even if a vendor has strong security measures, a single misconfigured integration on the customer’s side can expose the entire system. Regular third-party scanning is essential to catch these vulnerabilities before they become problems.
Supply Chain Attacks and Recent Examples
Recent incidents highlight how dangerous these vulnerabilities can be. For instance, in early 2025, attackers breached Salesloft’s SaaS environment and exploited OAuth tokens from just one integration. This allowed them to bypass traditional defenses and access Salesforce environments for over 700 organizations.
Later that year, the Shai-Hulud worm - a self-replicating npm malware - compromised 796 packages with over 20 million weekly downloads. The malware scanned for GitHub tokens and cloud API keys to spread further.
In March 2026, the hacking group ShinyHunters reportedly breached Woflow, a SaaS provider for major companies like Uber, DoorDash, and Walmart, claiming to have stolen hundreds of millions of records. Meanwhile, the 2023 MOVEit attack affected more than 2,700 organizations and exposed sensitive data for nearly 93 million individuals across industries like healthcare, finance, and government.
| Attack | Year | Impact | Attack Vector |
|---|---|---|---|
| Salesloft-Drift | 2025 | 700+ organizations compromised | OAuth token exploitation |
| Shai-Hulud Worm | 2025 | 796 packages, 20M+ weekly downloads | Self-replicating npm malware |
| MOVEit | 2023 | 2,700+ organizations, 93M individuals | Zero-day vulnerability exploitation |
| AT&T/Snowflake | 2024 | 110M+ customer records exposed | Stolen credentials, no MFA |
Insecure APIs and Data Flow Vulnerabilities
APIs are the glue that holds SaaS ecosystems together, but they’re also prime targets for attackers. Organizations have reported a 120% year-over-year increase in new integrations within Microsoft environments. Each new connection creates another potential entry point for unauthorized access or data theft.
The problem with API security often goes beyond basic encryption or authentication. Many OAuth tokens operate as "bearer tokens", meaning anyone who has them can gain access - bypassing multi-factor authentication (MFA) and single sign-on protections. These tokens frequently have overly broad permissions and no expiration dates, leaving them as long-term vulnerabilities.
Non-human identities, like service accounts, bots, and API keys, introduce additional risks. These accounts often have elevated privileges but lack safeguards like passwords or MFA, making them easy targets for attackers aiming to move laterally within systems. The growing use of AI agents with long-lived tokens has only made these risks harder to detect, emphasizing the need for automated scanning to maintain visibility and security.
Steps to Implement Third-Party Vulnerability Scanning
Mapping the SaaS Ecosystem
Before diving into vulnerability scanning, it’s essential to get a clear picture of your SaaS environment. On average, organizations use over 80 SaaS applications, but procurement lists often miss many of them. Employees can easily activate tools - like AI assistants, productivity apps, or collaboration platforms - without IT’s approval.
To build a complete inventory, gather data from sources such as accounts payable systems, single sign-on providers (e.g., Okta), OAuth grants, cloud marketplace subscriptions, and network egress logs. This will help uncover where your data actually flows. Don’t forget about "fourth-party" relationships - these are the vendors your vendors rely on, and they can introduce significant risks that must be accounted for. Create a data flow map to visualize how sensitive information moves between your organization, primary vendors, and third-party connectors. As one security expert put it:
"You cannot manage what you cannot enumerate. A vendor 'list' owned by procurement is rarely sufficient because it misses freeware, internal 'click-to-buy' SaaS, and embedded services." – CyberProof
Once your inventory is complete, categorize vendors into tiers based on their access to data and their importance to your operations. For example, Tier 0 vendors with admin access to production systems require the most scrutiny, while Tier 3 tools that pose minimal risk need less monitoring. With your internal inventory sorted, shift your focus to external assets that could expose your system.
Scanning Public-Facing Assets
After mapping your ecosystem, the next step is to scan the external attack surface - this includes domains, subdomains, cloud configurations, and internet-facing APIs. Many organizations overlook vendor-managed subdomains, such as branded support portals or API endpoints, which fall under your primary domain but are controlled by third parties.
Automated tools should continuously monitor for vulnerabilities in software versions, databases, cloud storage, and API keys. The threat landscape evolves daily, and new vulnerabilities appear all the time. Go beyond your own infrastructure and assess your vendors’ public-facing assets. Use outside-in security ratings to identify issues like expired SSL certificates, unpatched servers, or leaked credentials on the dark web. As one security leader noted:
"The risk is no longer limited to what you deploy directly. It is what your vendors expose through your identity, domains, and trust relationships." – Snapsec
Prioritizing and Fixing Risks
Once vulnerabilities on public-facing assets are identified, prioritize them based on their potential business impact and how feasible they are to address. Consider factors like whether public exploit code exists, if the vulnerable code is accessible in your environment, and the potential consequences of a breach. For instance, a critical flaw in a Tier 0 vendor handling customer payment data requires immediate attention, while a medium-severity issue in a Tier 3 marketing tool can be addressed later.
Collaborate with vendors to define clear remediation timelines in SaaS terms and services. Specify how quickly they must patch critical vulnerabilities and when they need to notify you of security incidents. Include "right to audit" clauses to verify their security measures. For integrations, update to patched versions, apply temporary fixes, implement compensating controls (like stricter input validation), or remove the vulnerable dependency altogether.
To streamline the process, integrate scanning tools with ticketing systems to automatically create tasks and generate pull requests for vulnerable dependencies. Conduct quarterly OAuth audits to identify and revoke unused or "zombie" tokens from former employees or abandoned tools. This can reduce your attack surface by 30–40%.
If a vendor can’t resolve a critical issue within your required timeframe, establish a documented risk acceptance process. Assign a designated owner, set an expiration date, and implement specific compensating controls. Focus on continuous improvement by holding stakeholders accountable for accepted risks, ensuring that remediation efforts strengthen the security of your SaaS ecosystem over time.
Benefits of Third-Party Vulnerability Scanning for SaaS Supply Chains
These advantages play a key role in strengthening the interconnected SaaS environment described earlier.
Early Risk Detection and Attack Prevention
Vulnerability scanning helps identify security flaws before attackers can take advantage of them. These tools detect issues like expired SSL certificates, open ports, unpatched software, and misconfigured APIs in a vendor's public-facing systems. Early detection is crucial, especially when the average cost of a breach stemming from third-party or supply chain compromises reaches $4.91 million. Scanning also flags compromised OAuth tokens and unauthorized integrations, allowing for swift action such as revoking access or adjusting permissions. Advanced tools go further by establishing behavioral baselines for identities and APIs. This makes it easier to catch unusual activity - like an integration exporting data at odd hours - which could indicate a breach.
By addressing risks early, organizations not only reduce breach costs but also strengthen their ability to meet regulatory requirements.
Improved Compliance and Regulatory Support
Vulnerability scanning simplifies compliance with frameworks like SOC 2, ISO 27001, and GDPR by generating audit-ready documentation. Instead of rushing to gather evidence during an audit, these tools automatically log vendor monitoring activities and align security measures with specific controls, such as Encryption at Rest and Access Reviews. Modern regulations, including DORA and CMMC 2.0, emphasize ongoing vendor oversight. Regulators now ask questions like, "How quickly did you detect and respond to vendor risks?" rather than just, "Did you assess the vendor?".
Scanning also aids in Privacy Impact Assessments (PIAs) by mapping data flows to third parties, ensuring compliance with regional laws such as CCPA and GDPR. With companies managing an average of over 80 SaaS software solutions, manual compliance tracking becomes impractical. As CM Alliance puts it:
"Always-on, audit-ready vendor oversight is a ticket to market".
Real-time monitoring ensures compliance efforts are directly tied to actionable security measures.
Real-Time Visibility into Security Status
Continuous scanning provides a real-time snapshot of your SaaS supply chain's security health. Unlike annual assessments, which only offer a limited view, real-time monitoring reduces the time attackers can linger in your systems by identifying compromised integrations and suspicious behavior as they happen. Given the fast pace of data exchange, manual monitoring simply can't keep up.
When incidents occur, real-time visibility allows security teams to trace the full attack path across identities and permissions, pinpointing what was accessed and what might still be vulnerable. This capability also enables immediate responses, such as revoking compromised OAuth tokens or isolating risky integrations. Dave Shackleford, Founder and Principal Consultant at Voodoo Security, emphasizes:
"Continuous vendor monitoring is no longer about predicting every breach, it's about shortening the time between vendor failure and organizational response".
Tools and Platforms for Third-Party Vulnerability Scanning
Common Solutions for Vulnerability Scanning
Choosing the right tool to protect your SaaS ecosystem is a crucial step in managing third-party risks. Several platforms have been developed to address the challenges of SaaS supply chain security, each offering distinct features.
Panorays combines automated assessments, continuous monitoring, and remediation workflows. Its AI-driven "Risk DNA" provides context-aware risk scoring, earning it recognition as a Leader in The Forrester Wave™: Cybersecurity Risk Ratings Platforms Q2 2024. Users have noted a 99.8% accuracy in risk ratings and an 80% reduction in vendor onboarding time.
Zscaler focuses on scanning SaaS platform connections through API integrations with platforms like Microsoft 365, Slack, and Salesforce. This allows it to detect risky third-party app permissions, enabling organizations to revoke excessive access before it can be exploited.
ThreatNG excels in external attack surface management, using an A–F grading system to evaluate feasibility, likelihood, and impact. It identifies outdated technologies and misconfigured cloud services, helping customers uncover 35% more internet-connected assets.
Contrast Security takes a unique approach with Software Composition Analysis (SCA) that incorporates runtime context. This helps identify if a vulnerable third-party library is actively used, reducing false positives. Research shows that over 18% of vulnerabilities stem from third-party libraries.
These tools each bring a distinct perspective to securing SaaS supply chains, offering organizations a range of options to strengthen their defenses.
The Role of All SaaS Software Directory

In addition to specialized scanning tools, a centralized resource can simplify the process of choosing secure vendors. The All SaaS Software Directory, curated by John Rush, serves as a comprehensive resource for evaluating SaaS solutions. It covers categories like software development, security, and enterprise tools, featuring well-known platforms like Salesforce alongside newer options.
This directory helps organizations identify SaaS products with strong security credentials while also offering vendors a way to gain visibility. By streamlining the search process, it allows security teams to efficiently evaluate solutions and build a supply chain that prioritizes security from the outset.
Conclusion
Shifting from annual reviews to continuous scanning isn't just a recommendation - it's a necessity. With 30% of data breaches tied to third parties and the costs of breaches remaining high, one thing is clear: your security is only as strong as your weakest vendor.
The pace of SaaS integrations has outstripped the capabilities of static assessments, making continuous monitoring essential. Organizations are seeing a staggering 120% annual increase in new integrations within Microsoft environments, rapidly expanding their attack surfaces beyond what manual reviews can handle. As highlighted earlier, SaaS ecosystems move at speeds that traditional methods simply can't keep up with. Dave Shackleford, Founder and Principal Consultant at Voodoo Security, sums it up perfectly:
"In today's environment, continuous vendor monitoring is no longer about predicting every breach, it's about shortening the time between vendor failure and organizational response."
Continuous scanning turns vendor risk management into an active security measure. It uncovers the hidden connections - OAuth tokens, API integrations, and service accounts - that often bypass IT oversight and create potential vulnerabilities. Unlike traditional software supply chain issues that require lengthy fixes, SaaS risks can often be addressed immediately by revoking tokens or adjusting permissions. By automating discovery, enforcing least privilege for integrations, and integrating alerts into existing ticketing systems, organizations can significantly reduce their exposure and stop breaches before they escalate.
The threat landscape is evolving fast. Attackers are increasingly focused on reusing valid OAuth tokens and exploiting API integrations to move laterally within SaaS environments. Waiting to act means relying on reactive incident responses, which can be costly and damaging. As CM Alliance aptly stated:
"If you build SaaS in 2026, vendor risk is product risk."
These developments highlight why continuous scanning is no longer optional - it’s a cornerstone of modern SaaS security, giving organizations the tools to stay ahead of supply chain vulnerabilities.
FAQs
What’s the difference between third-party scanning and a vendor questionnaire?
Third-party scanning involves using automated tools to pinpoint a vendor's cybersecurity weaknesses at a specific moment. On the other hand, vendor questionnaires are manual assessments designed to evaluate a vendor's security measures, compliance efforts, and operational protocols.
While scanning zeroes in on technical vulnerabilities, questionnaires offer a broader view of policies and risk management practices. Together, these methods work hand-in-hand to provide a more complete approach to managing third-party risks.
How can we find and remove risky OAuth tokens and “shadow” SaaS apps?
Organizations can better manage risky OAuth tokens and shadow SaaS apps by ensuring they have a clear view of all connected applications and their permissions. To do this, consider using third-party security tools that can spot tokens that are overprivileged, no longer in use, or persist unnecessarily. It’s also important to regularly audit OAuth-connected applications through identity providers such as Okta or Google Workspace. This allows you to revoke permissions that could pose a risk. Keeping an eye on SaaS integrations, API activity, and any unusual permission requests is another key step in identifying shadow apps and minimizing vulnerabilities within the SaaS supply chain.
Which vulnerabilities should we fix first across vendors and integrations?
When tackling vulnerabilities, it's essential to rank them based on severity scores, such as those provided by the Common Vulnerability Scoring System (CVSS). High-severity vulnerabilities, especially in third-party dependencies and integrations, should be your top priority. These issues often pose the greatest risk of exploitation and can significantly compromise your system's security. Addressing them quickly helps reduce potential threats and strengthens your overall defense.
