Continuous vendor risk monitoring uses automated tools to track third-party risks in real time - covering areas like security, compliance, finances, and operations. Unlike annual reviews, which leave gaps, this approach constantly identifies issues like data breaches, expiring certifications, or financial instability.
Key Takeaways:
- Why It Matters: Vendor-related breaches doubled in 2025, with detection taking an average of 277 days. Continuous monitoring reduces response time by up to 73%.
- How It Works: Automated systems collect data from APIs, threat feeds, and breach databases, triggering alerts for risks like vulnerabilities or credit rating changes.
- Risk Categories: Tracks cybersecurity, compliance, financial stability, operational continuity, reputation, strategy alignment, and ESG factors.
- Benefits: Improves risk visibility, ensures compliance with regulations like GDPR, and reduces costs by automating manual processes.
This method transforms vendor risk management from periodic checks into a real-time, proactive strategy, helping businesses stay secure and compliant.
Continuous Vendor Risk Monitoring: Real-Time Cyber Risk Visibility with Bitsight
sbb-itb-e3aed85
How Continuous Vendor Risk Monitoring Works
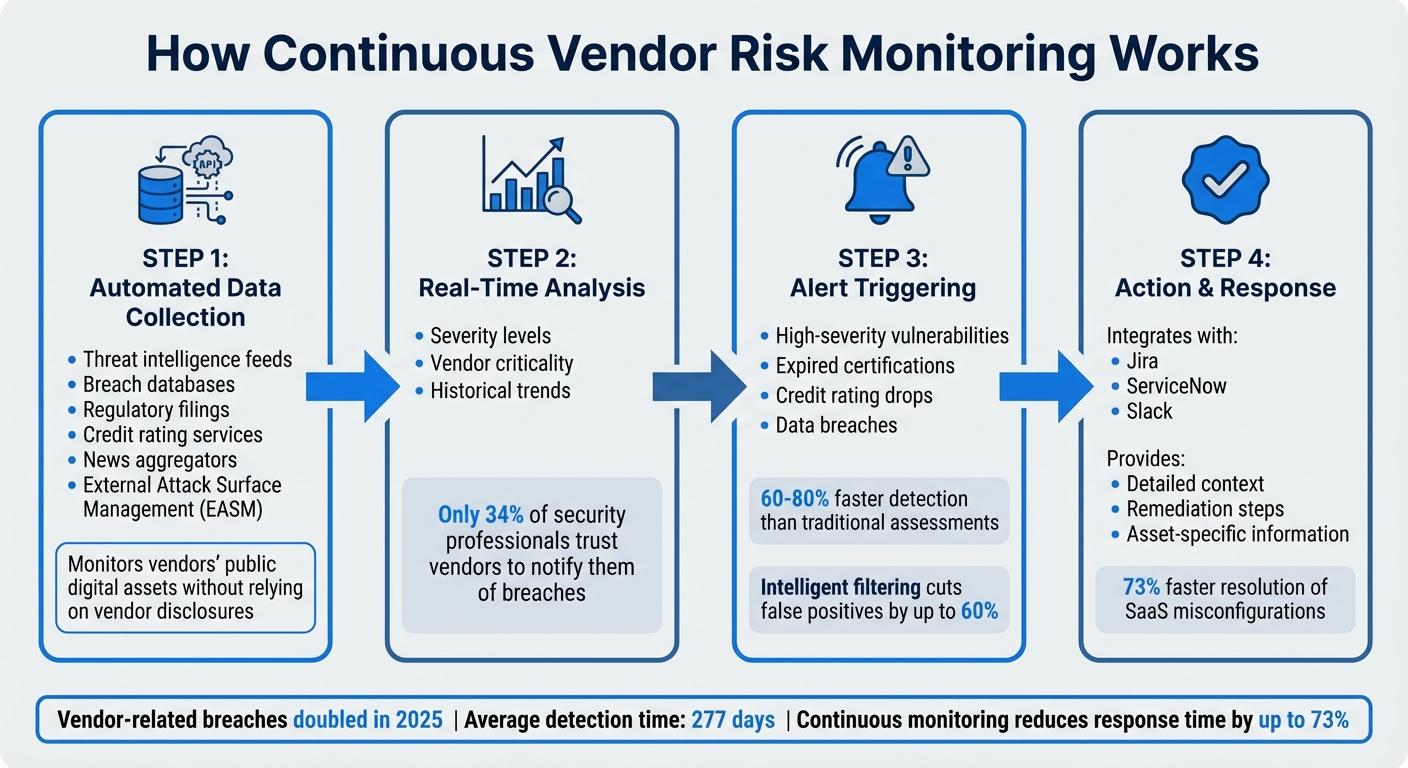
How Continuous Vendor Risk Monitoring Works: 4-Step Process
Continuous vendor risk monitoring uses automated systems to collect and analyze data based on predefined risk thresholds. These systems send real-time alerts whenever a vendor's risk profile changes. Unlike manual reviews that occur months apart, this approach helps identify issues like expiring security certificates, credit rating drops, or data breaches as they happen.
The process starts with automated data collection through APIs, pulling risk signals from sources like threat intelligence feeds, breach databases, regulatory filings, credit rating services, and news aggregators. External attack surface management (EASM) adds another layer by monitoring vendors' public digital assets - such as servers, domains, and cloud services - without relying on vendor disclosures. This external perspective is essential, especially since only 34% of security professionals trust vendors to notify them of breaches. By integrating multiple data sources, these best SaaS software solutions ensure no critical risk signals are overlooked.
Once data is collected, it’s analyzed for severity, vendor criticality, and historical trends. Alerts are triggered when thresholds are breached, such as identifying high-severity vulnerabilities or expired certifications. These tools can detect critical vendor incidents 60%–80% faster than traditional assessments. Advanced platforms also use intelligent filtering to cut down false positives by up to 60%, allowing teams to focus on the most pressing risks. Alerts not only flag issues but also provide detailed context, suggested remediation steps, and asset-specific information to speed up response times.
Risk Categories to Monitor
Continuous monitoring organizes risks into key categories, each addressing a specific aspect of vendor health. Seven core areas are typically tracked:
- Cybersecurity Risk: Covers data breaches, malicious attacks, missing patches, and expired certificates. These issues can compromise sensitive data and lead to legal trouble.
- Compliance and Regulatory Risk: Ensures vendors meet standards like GDPR, HIPAA, and SOC 2 to avoid fines and maintain compliance.
- Financial Risk: Assesses vendor stability by monitoring liquidity issues, negative cash flow, and credit rating changes, helping prevent financial disruptions.
- Operational and Business Continuity Risk: Focuses on service disruptions, downtime, and supply chain issues. Notably, 45% of organizations have faced third-party-related interruptions in the past two years.
- Reputational Risk: Tracks unethical practices, lawsuits, negative publicity, and public disputes to protect brand trust.
- Strategic Risk: Evaluates whether a vendor’s actions align with an organization’s long-term goals.
- ESG Risk: Monitors environmental, labor, and governance practices in response to growing accountability demands.
| Risk Category | Key Indicators | Why It Matters |
|---|---|---|
| Cybersecurity | Data breaches, phishing incidents, missing patches | Protects sensitive data and customer trust |
| Compliance | SOC 2 reports, GDPR/HIPAA status, investigations | Avoids legal penalties and maintains standards |
| Financial | Liquidity drops, credit rating changes | Prevents financial disruptions |
| Operational | SLA breaches, supply chain instability | Ensures business continuity |
| Reputational | Negative press, unethical practices | Protects brand reputation |
| Strategic | Goal misalignment, vendor direction changes | Supports long-term partnerships |
| ESG | Environmental violations, labor issues | Meets stakeholder expectations |
Data Sources for Monitoring
A wide range of external and internal sources fuels continuous monitoring, ensuring a detailed risk profile is built. Automated systems streamline data collection, removing the need for manual input. External sources include threat intelligence feeds, breach databases, credit rating services, regulatory filings, and news aggregators, all of which highlight vulnerabilities, financial risks, and compliance gaps.
Time-sensitive events, such as breach notifications, system outages, and certificate expirations, are monitored in real-time. Daily scans cover dynamic changes like new vulnerabilities or dark web mentions, while broader trends are reviewed weekly or monthly. Monitoring frequency depends on vendor risk levels: high-risk vendors may require real-time oversight, while lower-risk ones might only need weekly or monthly checks.
Real-Time Monitoring and Alerts
Real-time alerts allow organizations to act quickly on changes in a vendor’s risk profile, whether related to cybersecurity, financial stability, or compliance. These alerts integrate seamlessly with tools like Jira or ServiceNow, creating tickets, assigning tasks, and even isolating affected systems when necessary. Alerts also include detailed explanations of risks and recommended actions, helping teams resolve issues efficiently. For example, organizations using continuous monitoring tools address SaaS misconfigurations 73% faster than those relying on manual methods.
To maximize effectiveness, organizations must define clear thresholds for what constitutes a significant risk - such as a credit rating drop or a high-severity vulnerability - and establish escalation paths. This ensures that security, procurement, and legal teams are aligned on how to respond.
Periodic assessments still have their place, but they’re enhanced by this ongoing approach. As Nasir R from Atlas Systems puts it:
"The goal is actionable intelligence, not alert fatigue. Monitoring frequency and thresholds should balance risk awareness with team capacity to investigate and respond".
This structured alerting process forms the backbone of a robust vendor risk management strategy.
Steps to Implement Continuous Vendor Risk Monitoring
Assess Your Current Vendor Risk Management Framework
Start by evaluating your existing vendor risk management approach using the Vendor Risk Management Maturity Model (VRMMM). This framework outlines five levels of maturity:
- Initial: Ad hoc processes with no formal documentation.
- Repeatable: Basic assessments that differ across departments.
- Defined: Company-wide policies implemented with manual processes.
- Managed: Regular assessments supported by dashboards, though resource-heavy.
- Optimized: Fully automated and integrated, offering real-time insights.
Most organizations land between the Defined and Managed stages, meaning they have structured processes but lack real-time monitoring.
Next, audit your vendor inventory to ensure it’s comprehensive and centralized. Include details like service types, data access levels, and key stakeholders. Revisit your vendor tiering and scoring methods, and identify monitoring gaps by analyzing how often assessments are conducted and comparing them against continuous monitoring capabilities.
Ensure your internal security standards align with real-time data points. Clarify roles for stakeholders across procurement, legal, IT, and finance. For instance, if your policy requires vendors to maintain SOC 2 certification, a monitoring tool can alert you when a certificate is about to expire. Define your organization's risk tolerance and key performance indicators (KPIs) to align with your risk culture before selecting tools.
Once you’ve assessed your current framework, you’ll be ready to choose tools that support continuous monitoring.
Select Monitoring Tools and Platforms
Based on your assessment, choose a platform that integrates smoothly with your existing systems. The right tools can transform vendor risk management from a periodic task into an ongoing, proactive process. Look for platforms that automate key functions like vendor intake, risk scoring, evidence collection, and remediation tracking. Robust API connectivity is essential for integration with tools like Okta for vendor discovery, Jira or ServiceNow for ticketing, and Slack for real-time alerts.
Modern platforms often use AI to analyze vendor documents, such as SOC 2 reports, summarizing strengths and weaknesses automatically. Another critical feature is External Attack Surface Management (EASM), which provides continuous visibility into a vendor’s exposed assets and vulnerabilities without relying on vendor self-reporting. This is especially important since 46% of IT and business leaders reported data breaches linked to vendors after partnerships began.
When evaluating platforms, request live demos that showcase features like auto-discovery from identity providers and alert routing to ticket systems. Consider running a pilot program with a small group of high-risk vendors to refine the process before a full rollout. Pricing varies: enterprise platforms like OneTrust range from $40,000 to $500,000 depending on vendor count and complexity, while modular options like Vanta offer add-on pricing for advanced features. Resources like the All SaaS Software Directory (https://saassoftware.org) can help you compare solutions and find the best fit for your needs.
Once you’ve selected a platform, incorporate continuous monitoring into every stage of the vendor lifecycle.
Integrate Monitoring into Vendor Lifecycle Stages
To maximize effectiveness, embed monitoring at every phase of the vendor relationship - from onboarding to offboarding.
During onboarding, establish a risk baseline by documenting initial assessment scores, tracking SOC 2 expiration dates, and noting accepted risks. Include monitoring requirements in contracts, such as breach notification timelines (24–72 hours) and "right-to-audit" clauses for ongoing technical scans.
Use risk-based tiering to determine monitoring levels. Critical vendors require real-time oversight, while lower-risk vendors may only need automated annual reviews. Move beyond scheduled reviews by triggering reassessments for events like acquisitions, significant security rating drops (10+ points), or certification lapses. For smaller vendor portfolios, free tools like Google Alerts can help track vendor-related news using keywords like "breach", "acquisition", or "layoffs" paired with vendor names. Set automated reminders for contract renewals (90 days in advance) and certification expirations (30 days in advance).
During offboarding, ensure a clean exit by revoking SSO, API keys, and VPN access on the termination date. Request data destruction verification from critical vendors within 30–90 days, and archive contracts and assessments for 3–7 years to maintain compliance. By embedding monitoring into each stage, you create a continuous feedback loop that keeps vendor risks manageable throughout the entire relationship.
Benefits of Continuous Vendor Risk Monitoring
Building on the continuous data collection and alert mechanisms, these advantages directly improve vendor risk management strategies.
Better Risk Visibility and Mitigation
Traditional annual assessments leave a massive gap - 364 days without oversight between reviews. During this time, vendors could face breaches, adjust their security measures, or encounter compliance issues without your knowledge. Continuous monitoring eliminates these gaps by offering real-time updates on critical changes as they happen.
This method keeps track of risks across multiple areas: cybersecurity, financial, operational, and reputational. It also covers fourth-party risks, addressing concerns about subcontractors in SaaS environments, where risks can quickly ripple through the supply chain. Additionally, external attack surface intelligence provides constant insight into exposed assets and unresolved vulnerabilities, reducing reliance on vendors to self-report problems.
This shift turns third-party risk management from a static compliance task into an active, operational tool that supports daily decision-making. It's worth noting that only 34% of security professionals trust vendors to proactively inform them of a breach. Real-time insights like these also simplify compliance processes.
Meeting Regulatory Compliance Requirements
Regulatory expectations are evolving. The question is no longer just, "Did you assess the vendor?" but has shifted to "How swiftly did you detect and respond to vendor risk?". Continuous monitoring provides audit-ready evidence of ongoing oversight, aligning with the demands of regulators such as the Federal Reserve, OCC, and the UK Financial Conduct Authority.
The stakes are enormous. For instance, in May 2023, Ireland's data protection authority fined Meta $1.3 billion for GDPR violations. Under the Sarbanes-Oxley Act, executives risk fines of up to $1 million and 10 years in prison for certifying inaccurate financial reports. Continuous monitoring helps organizations stay compliant by automatically tracking regulatory updates, license suspensions, failed audits, and certification expirations like SOC 2 or ISO 27001.
GDPR, for example, requires notification within 72 hours of discovering a breach. With vendor-related breaches doubling year-over-year, as noted in the 2025 Verizon Data Breach Investigations Report, continuous monitoring ensures timely reporting and avoids penalties for non-compliance. It’s no surprise that 64% of organizations now rely on centralized or federated governance models for Third-Party Risk Management, enabling real-time visibility. This reflects a growing trend where compliance monitoring integrates with exposure management and identity-risk programs, delivering unified reporting for boards.
Cost Savings and Efficiency Gains
The financial benefits of continuous monitoring are hard to ignore. Sixty-one percent of companies reported a third-party breach in the past year, marking a 50% increase since 2021. Vendor-related breaches also raise total costs by 5%, highlighting the financial risks tied to third-party incidents.
Automation is a game-changer here, cutting down on manual, labor-intensive tasks. For instance, automated evidence collection can slash audit preparation time by up to 90%, freeing up engineering, security, IT, and HR teams to focus on strategic goals. Compliance automation can also reduce ongoing operational expenses by 30% to 40%.
Consider this: 88% of companies spent over $1 million on GDPR compliance, with 40% spending more than $10 million. A significant chunk of that cost came from manual evidence collection. Continuous monitoring keeps a permanent, exportable compliance record, eliminating the frantic "fire drill" costs tied to audit preparation.
There’s also the added benefit of potentially lowering cyber insurance premiums. Insurers increasingly view continuous monitoring as a critical factor in assessing risk. As vendor ecosystems grow to include hundreds or even thousands of partners, automation becomes the only scalable way to maintain effective oversight.
"The cost of continuous monitoring tools is typically far less than the impact of a single missed vendor breach."
- Nasir R, Atlassystems
Conclusion
Final Thoughts on Continuous Monitoring
Switching from yearly vendor assessments to continuous monitoring isn’t just about adopting new technology - it’s a major shift in how organizations safeguard themselves. Traditional, point-in-time reviews often leave dangerous blind spots, making businesses vulnerable to breaches, financial risks, and compliance issues that can arise at any time. According to the 2025 Verizon Data Breach Investigations Report, vendor-related breaches have doubled year-over-year, highlighting the growing risk of outdated assessment methods. Counting on scheduled reviews alone is no longer enough.
Continuous monitoring changes vendor risk management from a static, compliance-focused activity into a dynamic security measure. This approach prioritizes minimizing the time between a vendor's security lapse and your organization’s response. Companies using continuous monitoring tools resolve misconfigurations 73% faster and detect critical incidents 60%–80% quicker compared to those relying on annual assessments.
This real-time strategy not only tackles the regulatory and operational challenges mentioned earlier but also provides the audit-ready evidence and swift response capabilities required by today’s compliance standards.
Next Steps for Businesses
To strengthen your vendor risk management, start by analyzing your current framework in light of today’s threats. Focus on risk-based tiering - use real-time monitoring for high-risk vendors, while automating lower-risk checks. Update vendor contracts to include "right-to-audit" clauses and enforce breach notification deadlines of 24 to 72 hours.
When choosing a monitoring platform, resources like the All SaaS Software Directory (https://saassoftware.org) can help you find tools with automated evidence collection and real-time scanning features. Opt for solutions that integrate seamlessly with existing systems like SIEM platforms, ticketing tools (e.g., Jira, ServiceNow), and GRC software. This ensures alerts are automatically converted into actionable tasks. The ultimate goal is a system where vendor risks are addressed continuously, and your organization is always ready to act.
FAQs
What vendors should be monitored in real time?
Monitoring vendors in real time is crucial, especially those whose security, financial health, or operational risks could directly affect your organization. This often includes third-party providers offering essential services like SaaS platforms, cloud solutions, logistics, or data processing. It's particularly important to keep a close eye on vendors involved in areas like cybersecurity, financial services, or supply chain management, as any vulnerabilities or shifts in these sectors can lead to serious risks if not managed quickly.
How do you set alert thresholds without causing alert fatigue?
Set risk-based alert thresholds to ensure you're notified only about meaningful changes, cutting down on unnecessary noise. Focus on the most critical vendors by prioritizing alerts based on their importance to your operations. Leverage automated alerts to monitor when vendors’ security ratings drop below acceptable levels. By fine-tuning alert sensitivity and strategically setting thresholds, your team can stay informed about key risks without being buried in irrelevant updates.
What evidence should you keep to prove continuous oversight to auditors?
Maintaining documented evidence of regular risk assessments, control validations, and any identified issues - along with their resolutions - is crucial. This helps auditors confirm your consistent oversight. Examples of such documentation include reports, logs, and records that demonstrate ongoing monitoring and corrective actions.